NXP Security Solutions
Enable compliance and resilience with trusted security, tailored to your needs
Security must be designed in from the start—and sustained across the entire product lifecycle. With regulations such as the EU Cyber Resilience Act (CRA) raising the bar for cybersecurity, embedded designers need a clear way to establish trust at the silicon level and maintain it over time.
NXP EdgeLock® security provides a hardware‑based foundation that enables secure embedded designs from first boot through deployment and in‑field operation. Built on hardware roots of trust, EdgeLock technologies help protect critical security functions while supporting secure boot, device identity, protected communications, and runtime integrity across NXP MCUs, MPUs, and secure elements.
Combined with security enablement tools, lifecycle services, and certification‑ready capabilities, EdgeLock helps engineers right‑size security to their application, reduce integration effort, and support CRA‑aligned requirements for secure design, vulnerability handling, and long‑term resilience.
Featured Resources
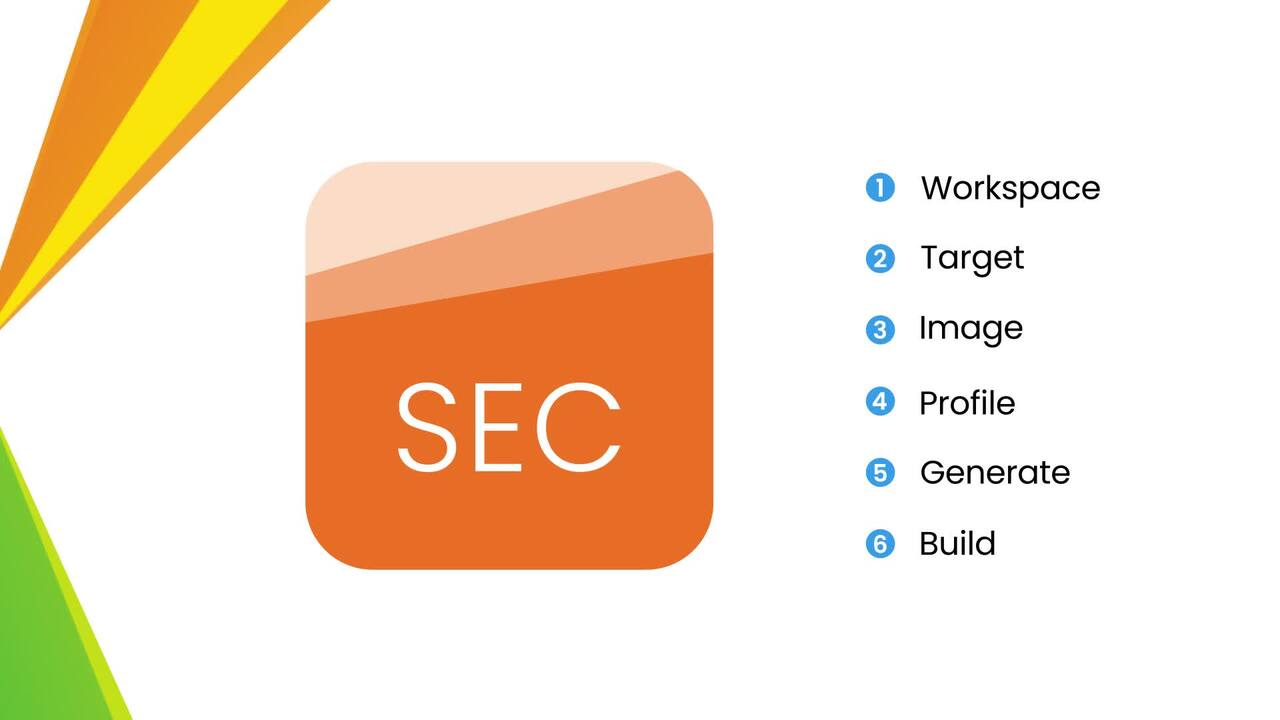
Six Steps to Secure Your IP with MCUXpresso SEC
This video explains the importance of IP protection and malware prevention in embedded development. Discover how NXP’s MCUXpresso SEC Tool enables secure bootloader setup in six simple steps.
Cyber Resilience Act (CRA): What it Means for Manufacturers
This video provides an overview of the Cyber Resilience Act (CRA)—a new EU regulation governing digital products—and explains how NXP’s MCX family helps manufacturers meet its requirements. It covers the CRA’s objectives, product categories and conformity obligations.

Secure Boot: Ensuring Trusted Software
This video covers the fundamentals of Secure Boot in embedded systems, showing how it ensures that only trusted, authorized software can run on a device. It explains the roles of authenticity and integrity, how digital signatures and hash functions work, and the practical steps involved in signing and verifying firmware.
FAQ
Even though no company can formally claim CRA conformance yet (notified bodies are not accredited), the CRA explicitly recognizes SESIP-, PSA- and Common Criteria-certified products as ready for conformance.In practice, these certifications, combined with our EdgeLock Assurance program and our IEC 62443 / ISO 21434-certified development processes, already provide customers with the level of assurance expected under the CRA and position NXP as a low risk, CRA ready supplier.
A product must comply with the CRA if all three conditions are met:
- It is a product with digital elements (hardware/software that processes, stores, or transmits digital data)
- It has direct or indirect logical or physical connectivity
- It is placed on the EU market (sold or made available as part of a commercial activity)
Additional guidance: The European Commission has published detailed technical descriptions for “Important” and “Critical” product classes under the CRA (Implementing Regulation (EU) 2025/2392), helping manufacturers determine whether their product falls into a higher risk category requiring stricter conformity assessment.
All categories meet the same essential cybersecurity requirements, but the proof mechanism differs:
- Default category: Self assessment
- Important Class I: Self declaration (if harmonized standards are applied)
- Important Class II: Third party conformity assessment
- Critical: EU certification (e.g., EU Common Criteria)
Secure Boot is essential, but not sufficient on its own for CRA compliance. Secure Boot contributes to protecting software integrity, which is required by the CRA, but CRA compliance also requires additional capabilities such as:
- Secure configuration
- Data protection
- Secure updates
- Access control
- Monitoring
- Vulnerability handling
- Lifecycle security processes
Each requirement must be addressed based on a product level risk assessment, and manufacturers must justify any measures that are not implemented.
CRA conformance means demonstrating that a product meets the Essential Cybersecurity Requirements of the Cyber Resilience Act and is therefore eligible for the CE mark, which is required for selling products in Europe.To achieve CRA conformance, manufacturers must:
- Conduct a risk assessment covering all essential cybersecurity requirements and justify how each requirement is implemented (or why it is not applicable).
- Implement a vulnerability management system and maintain a complete SBOM.
- Perform a conformity assessment and keep all supporting evidence for up to 10 years after placing the product on the market.
- Provide users with information on residual risk, intended use, support conditions, and vulnerability-handling processes.
- Prepare full technical documentation (standards, tests, evidence).
- Sign the Declaration of Conformity (DoC) and affix the CE mark.
- A product can only be considered CRA conformant when all these steps have been fully completed.